As the workforce grows, grouping employees by role and risk determines who can access critical systems; poor segmentation lets permissions creep, slowing response and raising security gaps.
Workforce leaders often assume that simply assigning roles is enough to keep critical systems safe, yet many organizations still see permission sprawl that hampers agility and creates hidden security risks. Operators juggling daily schedules, founders scaling rapidly, and HR or finance teams managing talent all confront the same blind spot: the lack of a disciplined approach to segmenting workers for access control. When the line between who needs to act and who merely observes blurs, permissions accumulate, response times suffer, and compliance becomes a guessing game. This article peels back the layers of that misconception, showing why traditional grouping methods fall short and what a more nuanced segmentation strategy can reveal. Now let’s break this down.
Why does precise worker segmentation matter for access control
When a company expands its headcount, the line between who needs to act on critical systems and who only observes can blur quickly. Precise segmentation creates a clear map that matches each employee’s responsibilities to the exact set of permissions required. This reduces the chance of accidental data exposure and speeds up incident response because the security team knows exactly who can intervene. At the same time, it supports compliance audits by providing a documented rationale for every access grant. A fast growing startup that relied on a single "employee" role soon found its engineers, finance staff and sales reps all sharing the same admin privileges, leading to delayed approvals and a breach scare. By applying a segmentation framework described by AIHR, the organization could separate high risk, medium risk and low risk groups, aligning technology controls with business risk and preserving agility.
What common misconceptions cause permission sprawl
Many leaders assume that assigning a job title automatically defines the right access level. In practice, roles evolve faster than policies, and a single title often masks a variety of functions. This misconception leads to permission sprawl, where privileges accumulate over time because new tools are added without revisiting the original assignment. Another false belief is that once a permission is granted it never needs to be reviewed. As teams shift projects, outdated rights linger, creating hidden security gaps. Research from ActivTrak shows that organizations that treat segmentation as a one time event see a 30 percent increase in access related incidents. The root cause is treating access control as a static checklist rather than a dynamic reflection of daily work patterns.
How can organizations build a nuanced segmentation model
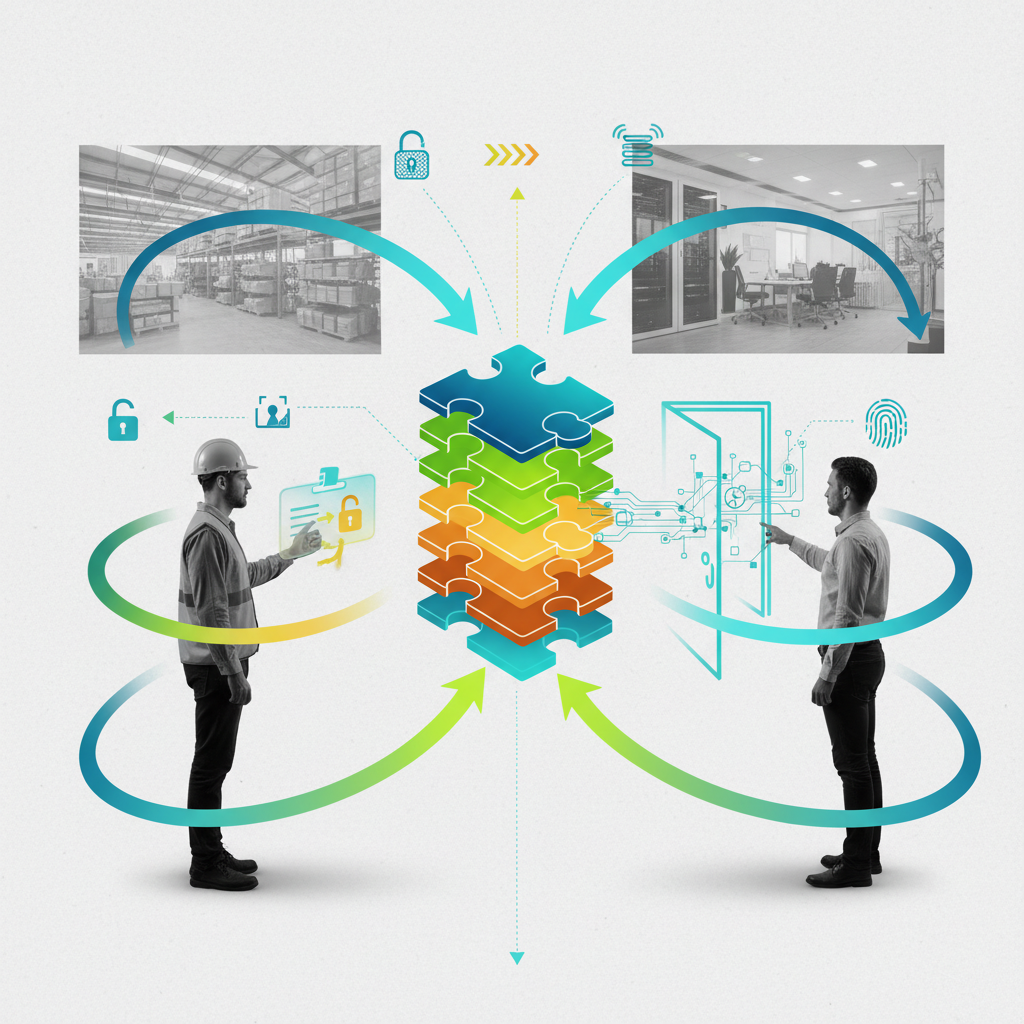
A robust model looks beyond job title and incorporates risk level, location, function and performance tier. First, map each employee’s core tasks and the data they touch. Next, assign a risk rating based on the sensitivity of those data flows. Finally, layer additional attributes such as remote versus on site work and contract versus permanent status. Tools like Delve AI can automate the data collection, while platforms such as Workhint help visualize the resulting groups and enforce policy through single sign on integrations. The tradeoff is between the effort to maintain the model and the reduction in security incidents. Organizations that invest in a multidimensional approach report faster onboarding, fewer permission errors and clearer accountability across the workforce.
What pitfalls slow teams when segmentation is poorly designed
When segmentation relies on overly broad categories, employees spend time requesting temporary access for tasks that fall outside their default group. This creates a bottleneck for managers and frustrates staff who feel they cannot get work done. Additionally, if the segmentation logic is hidden in spreadsheets, updates become error prone and audit trails disappear. A common error is to treat segmentation as a compliance checkbox rather than a living framework, leading to stale groups that no longer reflect the organization’s structure. The result is a cycle of workarounds, manual overrides and increased risk exposure. By keeping the model transparent and aligning it with daily workflows, teams can avoid these delays and maintain a smoother operational rhythm.
What does an optimal access control segmentation framework look like
An optimal framework balances granularity with manageability. It defines a limited set of clear segments – for example executive, high risk technical, standard operational and support – each with a documented permission matrix. The matrix links specific system actions to business outcomes, so any change in a role triggers a review of the matrix. Governance processes include quarterly reviews, automated alerts for orphaned permissions and a clear escalation path for emergency access. The framework also integrates with identity providers to enforce the segment definitions in real time, reducing manual provisioning. When designed this way, the organization enjoys faster onboarding, lower audit effort and a measurable decline in security incidents.
FAQ
How often should access permissions be reviewed after segmentation
Best practice is to conduct a formal review at least once each quarter. During the review, compare current employee attributes against the segmentation criteria and revoke any rights that no longer match. Adding automated alerts for changes in job function or location can prompt interim reviews between the quarterly cycles, ensuring the permission set stays aligned with real world responsibilities.
Can segmentation be applied across multiple business units with different risk profiles
Yes, the model can incorporate unit specific risk scores. Each unit defines its own sensitivity levels for data and processes, and the segmentation engine assigns employees to the appropriate risk tier based on both their role and the unit they belong to. This approach preserves a unified access control policy while respecting the unique compliance demands of each division.
What metrics indicate a successful worker segmentation for access control
Key indicators include a reduction in the number of emergency access requests, a lower count of orphaned permissions, and faster average time to grant legitimate access. Audit findings that show fewer violations related to excessive privileges also signal success. Tracking these metrics over time helps demonstrate the business value of the segmentation effort.
Workforce Segmentation and Access Control
When an organization expands, the number of roles, locations, and contracts multiplies. Each new participant adds a set of permissions that must be tracked, reviewed, and aligned with business risk. Without a single source of truth, teams rely on spreadsheets, email threads, and separate identity tools, which quickly become out of sync.
At a certain scale the ad hoc approach breaks down because updates are applied in isolated silos, duplicate entries appear, and audit trails are incomplete. The resulting permission sprawl slows response to incidents, creates compliance gaps, and forces manual reconciliation that diverts resources from core work.
A centralized workforce infrastructure provides a unified directory, role definitions, and automated policy enforcement. Platforms such as Workhint illustrate the type of system that consolidates identity data, segmentation rules, and access controls in one place, allowing teams to apply changes globally and maintain an auditable history.
Therefore, organizations that need reliable segmentation for access control must adopt a single, configurable platform rather than piecemeal solutions, ensuring that permission sets remain aligned with evolving roles and risk profiles.
Returning to the opening question, worker segmentation is not merely a catalog of titles but a dynamic alignment of responsibility, risk and context. The article showed that when segmentation is treated as a static assignment, permissions accumulate unnoticed and response time suffers. By continuously mapping tasks, data sensitivity and work conditions, organizations create a living map that guides each access decision and keeps the security perimeter tight without throttling agility. The practical insight is that segmentation should be refreshed whenever a role changes, a new tool is introduced, or a work pattern shifts; this habit turns permission sprawl into a manageable signal. In short, access control works best when it mirrors work, not when it forces work into a fixed label.
Leave a Reply